Hackers have exploited-and are presently continuing to make the most of- a now-patched 0-day vulnerability in a popular WordPress plugin to install backdoors and take over websites. The vulnerability impacts WP GDPR Compliance, a WordPress plugin that allows website owners to grow to become GDPR compliant. The plugin is one of the maximum popular GDPR-themed plugins on the WordPress Plugins directory, with over one hundred 000 active installs.
MORE SECURITY NEWS
Google’s automated fuzz bot has determined over 9,000 insects in the beyond two years. Russia: Now, absolutely everyone who makes use of a messaging app should be identifiable
Why are faux Elon Musk bitcoin scams going for walks rife on Twitter proper now? States set off National Guard cyber units for the US midterm elections. Around three weeks ago, attackers appeared to have discovered a vulnerability in this plugin and commenced using it to gain entry to WordPress websites and install backdoor scripts.
Initial reports about hacked websites have been made in any other plugin’s support forum, but that plugin turned out to have been set up as a 2-level payload on some of the hacked websites. After investigations led through the WordPress security team, the source of the hacks was eventually traced back to WP GDPR Compliance, which became the common plugin set up on all said compromised sites. The WordPress team eliminated the plugin from the respectable Plugins directory earlier this week when they identified numerous security problems inside its code, which they believed had been the purpose of the stated hacks.
However, the plugin was reinstated two days in the past after its authors launched version 1. Four 3, which contained patches for the suggested problems.
ATTACKS ARE STILL GOING ON
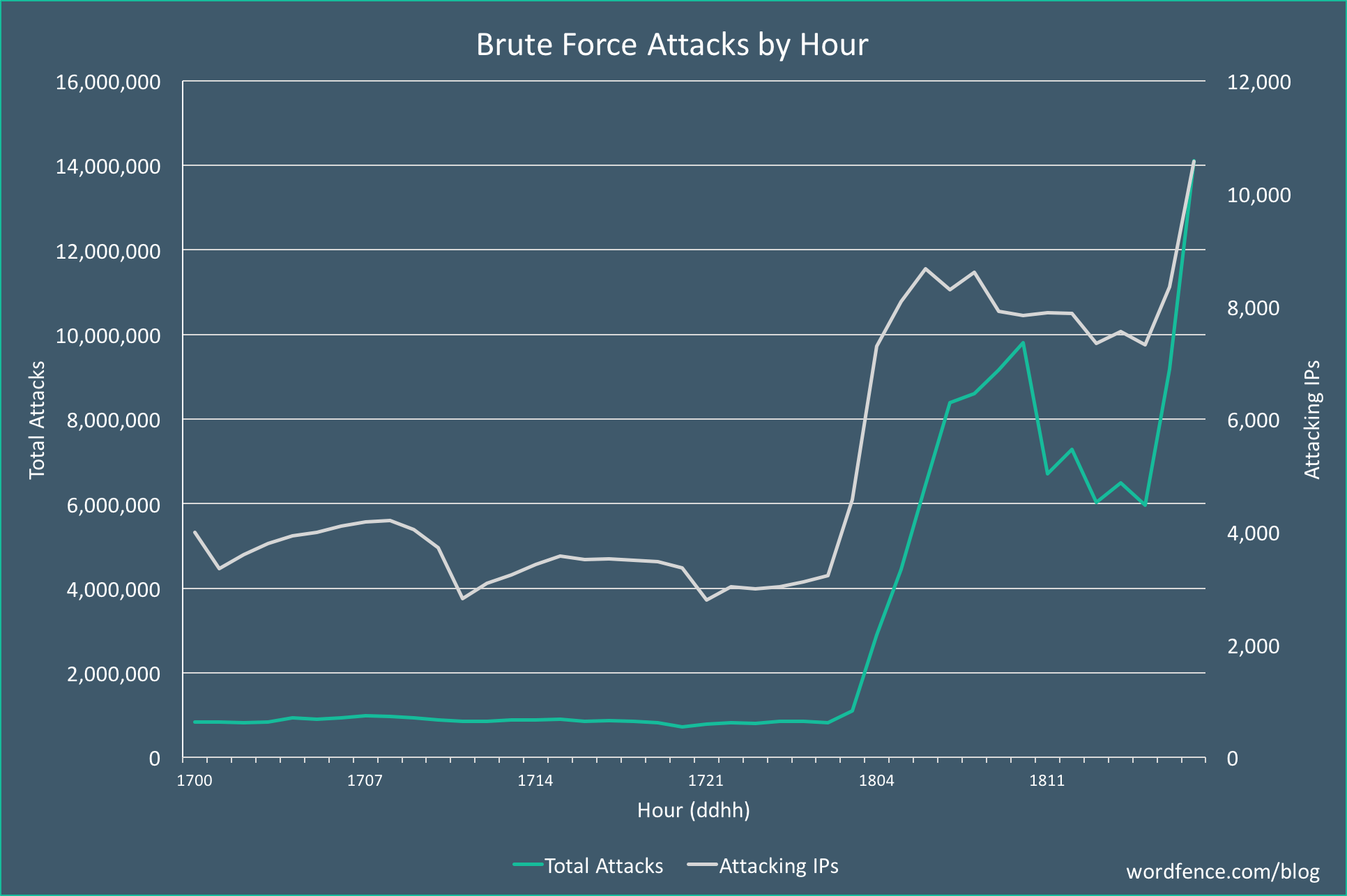
But no matter the fixes, attacks on websites are still targeting version 1. Four 2 and older are nonetheless occurring, consistent with safety specialists from Defiant, a corporation that runs the Wordfence firewall plugin for WordPress websites. The agency’s analysts say they’re persevering to discover attacks that try to exploit one of the said WP GDPR Compliance safety troubles. In unique, attackers target a WP GDPR Compliance trojan horse that allows them to make a name to one of the plugin’s inner features and exchange settings for each plugin and the complete WordPress CMS.
The Wordfence team says they have seen two styles of assaults the usage of this malicious program. The first scenario goes like this: Hackers use a computer virus to open the site’s consumer registration gadget. Hackers use the malicious program to set the default position for new money owed to the “administrator.” Hackers sign in to a new account, which automatically turns into an administrator. This new account is typically named “t2trollherten.” Hackers set again default user position for brand new debts to “subscriber.”
Hackers disable public consumer registration. Hackers log into their new admin account. They then continue to put in a back door at the site, as a record named wp-cache. Personal home page. This backdoor script (GUI pictured underneath) incorporates a file manager, terminal emulator, and a PHP eval() characteristic runner, and Wordfence says that “a script like this on a website can allow an attacker to install payloads similarly at will.”
wp-gdpr-plugin-backdoor.png Image: Defiant
But professionals also detected a 2d sort of assault, which doesn’t depend on developing a new admin account, which might be noticed using the hacked web page’s owners. This 2nd and supposedly greater silent approach entails using the WP GDPR Compliance trojan horse to feature a new assignment to WP-Cron, WordPress’s built-in project scheduler.
The hackers’ cron process downloads and installs the 2MB Autocode plugin, which attackers later use to add some other backdoor script on the website –additionally named wp-cache—personal home page, however, extraordinary from the onn above. But whilst hackers tried to make this 2d exploitation state of affairs more silent than the first, it turned into, in fact, this technique that led to the 0-day’s discovery. This passed off because, on some sites, the hackers’ exploitation routine did not delete the 2MB Autocode plugin. Site proprietors noticed a brand new plugin appeared on their websites and panicked.
It became, in fact, in this plugin’s WordPress guide forum that website owners first complained about approximately hacked websites, which led to the research that again led to the WP GDPR Compliance plugin.
ATTACKERS ARE STOCKPILING HACKED SITES
Right now, the attackers do not appear to be doing anything malicious with the hacked sites, according to the Wordfence team. Hackers are just stockpiling hacked websites. Wordfence has not seen them looking to deploy whatever malicious code through the backdoor scripts, including SEO spam, take advantage of kits, malware, or other sorts of badness. Site owners using the WP GDPR Compliance plugin nonetheless have time to replace or eliminate the plugin from their websites and ease any backdoors that have been left in the back of. They should do that before their site achieves success in terms of seek engine scores, which typically happens after Google unearths malware on their domains for the duration of its regular scans.
